🎯Basically, a serious flaw in a web tool lets hackers take control of servers.
The Flaw
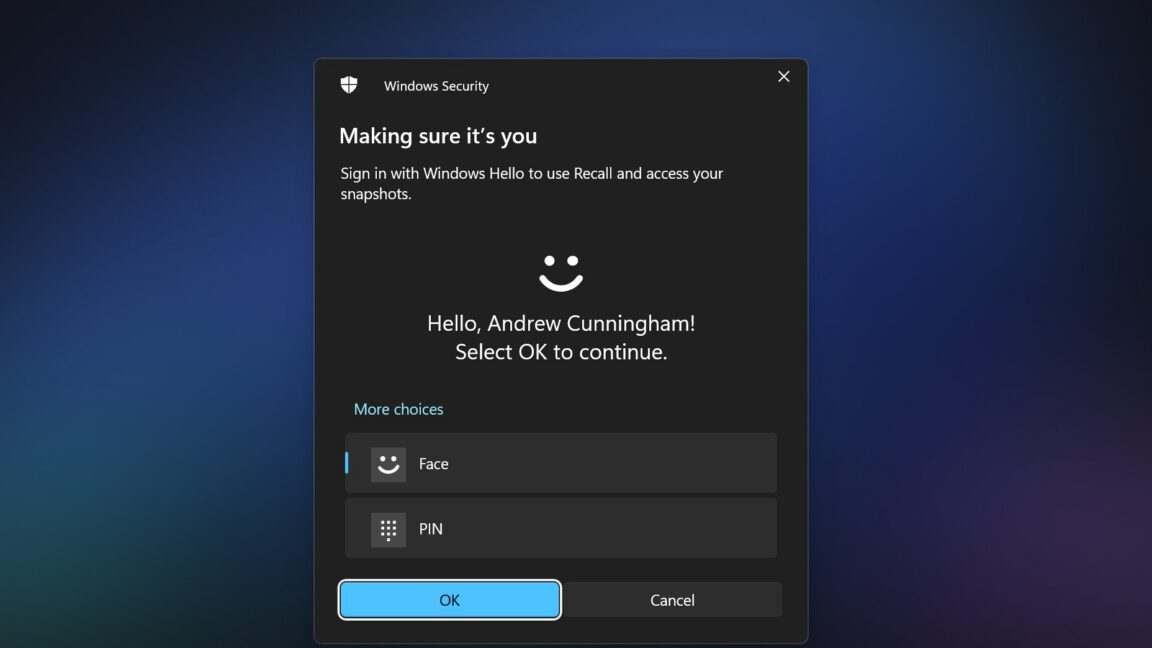
Pluto Security has identified a critical vulnerability in the open-source nginx UI web server configuration tool, known as CVE-2026-33032. This flaw has been under active exploitation since March 2026, raising significant concerns for users. The vulnerability relates to the software's support for Model Context Protocol (MCP) servers, which allows communication between nginx web servers and AI models through HTTP-accessible endpoints.
What's at Risk
The vulnerability exposes 12 MCP tools, including the ability to write configurations and automatically reload nginx, to any host on the network. An attacker can exploit this flaw with a single unauthenticated API call, leading to complete control over the nginx server. This could result in intercepting traffic, harvesting admin credentials, and even disabling the service.
Patch Status
The CVSS score for this vulnerability is a staggering 9.8, indicating its critical nature. A patch (version 2.3.4) was released on March 15, 2026, making it imperative for users to apply it immediately. For those unable to patch right away, a temporary workaround involves disabling MCP or restricting access to trusted IPs.
Immediate Actions
Security teams should prioritize applying the patch to mitigate risks. Additionally, they should review access logs for unusual configuration changes and consider auditing Server-Sent Events (SSE) endpoints to ensure robust security measures are in place.
Conclusion
This vulnerability serves as a reminder of the potential risks associated with AI integrations in web server management tools. As highlighted by Pluto Security, the rapid adoption of such integrations can inadvertently create new vulnerabilities. Organizations must treat these integration layers with the same scrutiny as core application security.
🔒 Pro insight: This vulnerability underscores the need for stringent security measures around AI integration points in web server configurations.