🎯Basically, a fake Slack download lets hackers control your computer without you knowing.
What Happened
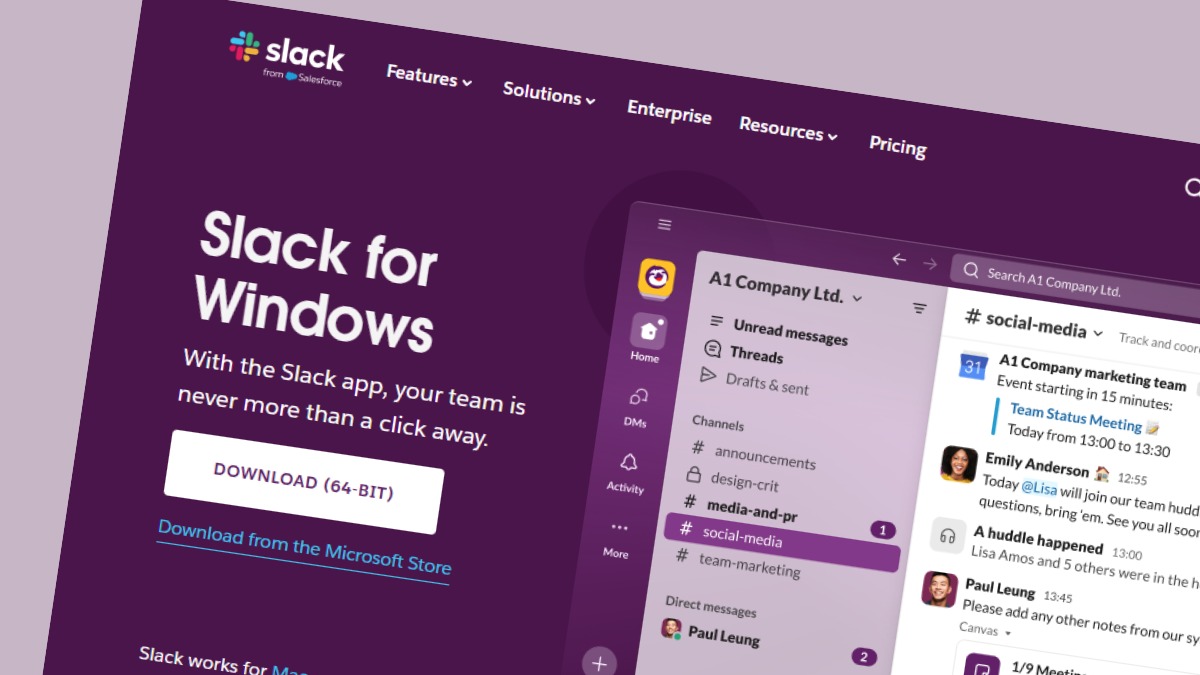
A recent cyber threat has emerged involving a trojanized Slack installer from a typosquatting website. This malicious download appears legitimate but secretly establishes an invisible desktop for attackers, enabling them to access user accounts and sensitive data without detection.
Who's Being Targeted
This attack primarily targets Slack users, which includes millions of individuals and organizations worldwide. With Slack being a common tool in workplaces, the potential for widespread impact is significant, especially for corporate networks that rely on Single Sign-On (SSO) systems.
How It Works
The attackers registered a domain that closely resembles the official Slack site, using slacks[.]pro instead of slack.com. When users click on the site, they are redirected to a download that appears to be a legitimate Slack installer. However, in the background, a malware loader is executed alongside the real Slack installation, creating an invisible session on the victim's machine.
Signs of Infection
Victims may notice no immediate signs of infection, as the trojan installs a working copy of Slack while simultaneously running malicious processes. The presence of files like svc.tmp in the %TEMP% folder and unusual network activity could indicate an infection.
How to Protect Yourself
To safeguard against this threat, users should:
Detection
- 1.Always download software from official websites.
- 2.Verify URLs carefully before clicking.
Removal
- 3.Run virus scans on any suspicious downloads.
- 4.Monitor network activity for unusual connections.
Technical Details
The malware loader operates by creating a hidden desktop session, allowing attackers to interact with the victim's machine without their knowledge. This method is particularly dangerous as it can facilitate financial fraud and unauthorized access to sensitive accounts.
Conclusion
If you have downloaded Slack from an unofficial source, especially from a domain ending in .pro, take immediate action. Remove the application and run a thorough security scan to check for any signs of compromise. Awareness and caution are your best defenses against such sophisticated attacks.
🔒 Pro insight: This campaign highlights the effectiveness of typosquatting and social engineering in exploiting trusted brands for malware distribution.



.webp)