🎯Basically, some hackers make simple mistakes that help stop their attacks.
What Happened
You might think that all hackers are highly skilled professionals, but that’s not always the case. Many malware attacks are surprisingly unsophisticated, often due to simple errors made by the attackers themselves. This post dives into how these blunders can help defenders thwart attacks before they cause any real damage.
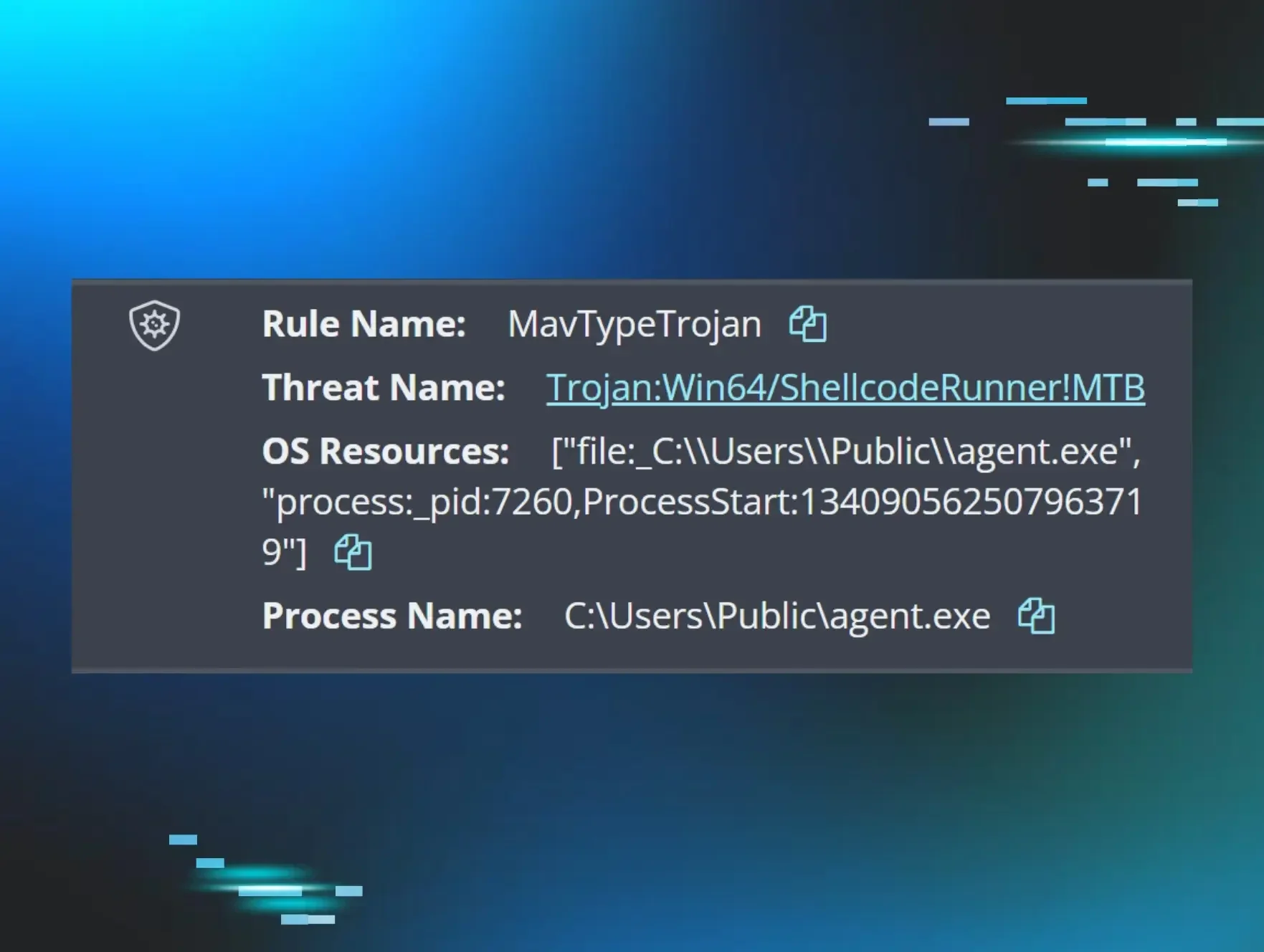
In the world of cybersecurity, there’s a common misconception that all threat actors possess advanced technical skills. However, many attacks are executed with basic tools and techniques. For instance, attackers might use malware that is poorly coded or filled with typos, making it easier for security systems to detect and block them. This reveals a critical gap in the perception of threat actors' capabilities.
Why Should You Care
Understanding the nature of these unsophisticated attacks can empower you to take better precautions. If you think hackers are always clever, you might underestimate the importance of basic security measures. Just like locking your front door can deter a burglar, simple cybersecurity practices can protect your data from these less-skilled attackers.
The key takeaway here is that you don’t need to be a tech genius to defend against cyber threats. By implementing basic security protocols, you can significantly reduce your risk of falling victim to malware. Remember, even the most basic defenses can stop a poorly executed attack.
What's Being Done
Experts in cybersecurity are constantly analyzing these unsophisticated attacks to improve defense strategies. Organizations are focusing on enhancing their detection systems to catch even the simplest forms of malware. Here are some actions you can take right now:
- Regularly update your software to patch vulnerabilities.
- Use strong, unique passwords for all your accounts.
- Educate yourself and your team about common cyber threats and how to recognize them.
Experts are watching for trends in how attackers adapt to these defenses. As they become aware that their unsophisticated methods are being thwarted, they may try to evolve their tactics. Stay informed and proactive to keep your systems secure.
🔒 Pro insight: The prevalence of unsophisticated malware highlights the need for continuous education on basic cybersecurity practices among users.