🎯Basically, this article shares tips for using passkeys to make logging in safer and easier.
What Happened
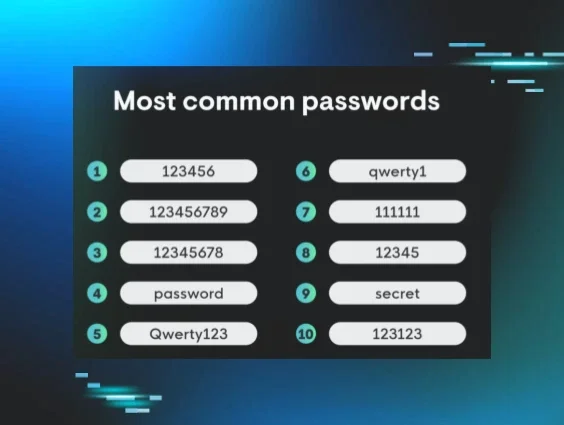
In the evolving landscape of cybersecurity, traditional passwords are increasingly vulnerable to attacks. Recognizing the need for a stronger solution, organizations are turning to passkeys as a more secure alternative. This article serves as a playbook for Chief Information Security Officers (CISOs) aiming to implement passkeys effectively.
How Passkeys Work
Passkeys leverage FIDO2 public key cryptography to enhance security. Each user is assigned a unique public-private key pair. The public key is stored on the server, while the private key remains secure on the user’s device. During login, a challenge is sent to the device, which is signed with the private key. This method ensures that no credentials are transmitted, making them resistant to phishing attacks.
Benefits of Passkeys
Organizations and employees can reap numerous benefits from adopting passkeys:
- Enhanced Security: By eliminating passwords, the risk of credential-based attacks is significantly reduced.
- Convenience: Users no longer need to remember complex passwords, streamlining the login process.
- Reduced Help Desk Requests: Fewer password-related issues lead to decreased support tickets, allowing teams to focus on other tasks.
Considerations and Caveats
Implementing passkeys is not without its challenges. Organizations should consider:
- The existing infrastructure and compatibility with current systems.
- How passkeys will be stored and managed.
- Ensuring users are educated on safeguarding their access.
Success Factors for Implementation
Successful passkey implementation hinges on several key factors:
- Internal Partnerships: Collaborate with various teams to ensure a smooth rollout.
- User-Centric Approach: Keep the user experience in mind throughout the process.
- Clear Communication: Maintain transparency about the benefits and changes.
How We Can Help
To assist organizations in this transition, a comprehensive playbook has been created, featuring an implementation guide, FAQ, and templates for project managers. This resource aims to simplify the process and address common challenges encountered during the rollout of passkeys.
🔒 Pro insight: The transition to passkeys represents a significant shift in authentication strategies, emphasizing the need for robust user education and support.